Table of Contents
There are several steps to integrate IoT devices into a secure environment. Every day, businesses rely on IoT technology to fuel the connectivity between their devices and the internet. While IoT offers convergence and full connectivity between devices, the technology can also attract fraudulent hackers or external threats. As a business owner, you need to take the proper measures and precautions to integrate, install, and monitor IoT devices securely. This way, you can reduce risk, optimize your network, and secure your operating environment. Read on and learn how to integrate IoT devices into a secure environment.
Employ Device Discovery
First off, employ device discovery to integrate into a secure environment of IoT devices. Start this process by documenting all the different types of IoT devices that are connected to your network. Then, organize an up-to-date inventory report with all included security solutions.
You should also take note of the manufacturer, model ID, operating system, and configuration on each device. Once you have documented the specifications, you’ll have a better understanding of the entire risk profile and behavior of each network-connected device. Since it is known to seriously streamline processes, device discovery is also known as a major productivity hack to follow this year. Certainly, employ device discovery to integrate your secure environment.
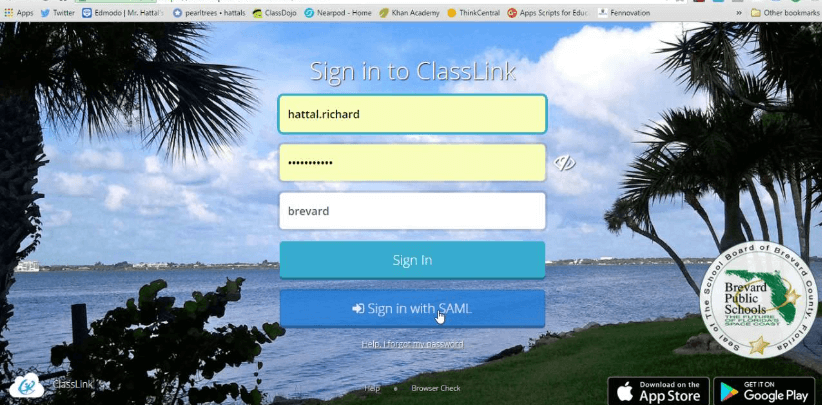
Enforce Strong Passwords
In addition, you should enforce strong passwords when integrating IoT devices into a secured environment. Change your default passwords once they are accessed for the first time. Also, make sure you are constantly working with difficult, hard-to-guess passwords and access codes. After all, complicated passwords prevent data breaches throughout your network.

Plus, strong unique passwords fortify devices, defend against malicious hackers, and block software designed to infiltrate your IoT environment. Or, you can upgrade your password protection strategy with multi-factor authentication. Surely, you should enforce strong password credentials to integrate your IoT devices into one secured environment.
Find A Powerful Integration Tool
Then, find a powerful integration tool to integrate all of your IoT devices into a secured environment. Implement a tool that can conduct over the air software updates across your IoT environment. For example, you can use JFrog’s iot device manager to update, monitor, control, and secure remote IoT devices at scale. It can also support extensive control to streamline virtual device management from anywhere in the world.
With these solutions, you can leverage real-time monitoring to visualize your IoT device’s resources, status, and data. This way, you can promote high visibility across various fleet versions and locations. Definitely, utilize an advanced integration tool to integrate your IoT devices in a secure environment.
Segment Your Network
In addition, segment your network to integrate your IoT device environment securely. Design your segmented network to communicate and operate independently. Then, connect your devices and sub-networks to stay protected against external attack. Of course, these segmented networks are able to enforce security measures at a much higher, more reliable level.

After all, this networking feature minimizes damage, data loss, and the size of the attack area. Plus, network segmentation helps organizations focus on security without sacrificing valuable resources. For sure, you should integrate your IoT device environment securely with network segments.
Test IoT Devices Frequently
Now, you should test your IoT devices frequently throughout integration. Conduct penetration testing on a weekly basis to evaluate each device’s protection. These forward-looking tests safeguard your devices against errors, issues, bugs, or unseen defects. In addition, you should analyze software and hardware solutions with in-depth functionality tests. After this evaluation process, integrate the solutions into your IoT network to maintain stability and security.
Then, monitor your devices for potential vulnerabilities and security risks. Once you have identified and solved the problem, you can deploy your IoT devices for public use. Of course, frequently test your IoT devices to integrate your environment securely.
There are several steps to integrate IoT devices into a secure environment. First, you should employ device discovery to gather specifications, Then, enforce strong passwords and prevent data breaches. You may even want to expand your basic password strategy to include two (2FA) or multi factor authentication (MFA) as well. Next, find a powerful integration tool to monitor, manage, and optimize your IoT network. Also, segment your network and enhance security.
This is especially true when working with enterprise IoT devices, networks, and platforms. Of course, test your IoT devices frequently to identify and address vulnerabilities. Follow the points highlighted above to learn how to integrate your IoT devices into a secure environment.