Table of Contents
What is Penetration Testing?
Penetration testing, or “pen testing”, is the process of attempting to circumvent the security features of a computer system or network. It is essentially an act of simulated cyber espionage and is often used to identify and fix vulnerabilities in a system before they can be exploited by criminals or other malicious actors. AWS offers a wide variety of services that can be used for pen testing, making it an attractive option for businesses and organizations of all sizes.
Pen-testing in the cloud presents its unique challenges and opportunities, as compared to traditional on-premises systems. In this article, we’ll take a comprehensive look at what pen-testing in AWS entails, what you can (and can’t) test for, and how to go about doing it.
Why AWS Penetration Testing Matters
AWS is a popular choice for businesses and organizations of all sizes due to its scalability, flexibility, and cost-effectiveness. However, because AWS is a cloud-based platform, it presents some unique challenges from a security perspective. In particular, the shared responsibility model in terms of security means that AWS customers are responsible for securing their data and applications, while Amazon is responsible for providing a secure infrastructure.

As organizations increasingly move their workloads and data to the cloud, it’s more important than ever to ensure that these assets are well-protected. After all, a successful attack on a cloud-based system can be just as devastating as one carried out against an on-premises system. Sometimes it is difficult to identify and fix the vulnerabilities on time. Regular AWS penetration testing can help with this by providing visibility into potential weaknesses in an AWS environment so that they can be addressed before they are exploited.
It is also one of the most attractive targets for cyber-attacks, due to its high visibility and a large number of potential victims. As such, it is important for businesses that use AWS to ensure that their systems and data are secure. Pen-testing can help identify vulnerabilities in an AWS environment so that they can be fixed before attackers have a chance to exploit them.
For example, an attacker who gains access to an AWS account could potentially launch attacks on other customers sharing the same underlying infrastructure. Or, an attacker could take advantage of misconfigured security settings to gain unauthorized access to sensitive data.
In short, pen-testing your AWS environment is a vital part of ensuring the security of your cloud-based systems and data.
What types of Pen-Testing can be performed in AWS
Several different types of penetration tests can be performed in AWS. These include:
- Discovery scans – these scans identify potential targets for attack, such as open ports and vulnerable services. These tests are designed to identify all accessible resources within an AWS environment. This includes public IP addresses, DNS names, and exposed ports and services.
- Vulnerability scans – These scans can be done to find the Vulnerabilities in the system that need to be fixed.
- Exploitation attempts – these are actual attacks on systems and applications, using known exploits.
- Social engineering – this is the process of trying to trick users into revealing sensitive information, such as passwords or credit card numbers.
These scans can be performed by your internal IT security team or you can evaluate a penetration testing provider that can do this job for you.
WHAT CAN’T BE TESTED IN THE AWS CLOUD?
Not all aspects of an AWS environment can be tested using penetration techniques. For example, it is not possible to test the physical security of an AWS facility or the security of the AWS network infrastructure. Additionally, some types of tests may be prohibited by AWS terms of service or other agreements.

If you plan to conduct penetration testing in your AWS environment, it is important to consult the AWS customer support policy first. This policy outlines what types of tests are permitted and how customers should go about requesting permission to conduct them. Additionally, the policy includes some guidelines that must be followed when conducting penetration tests to minimise disruption to other AWS customers.
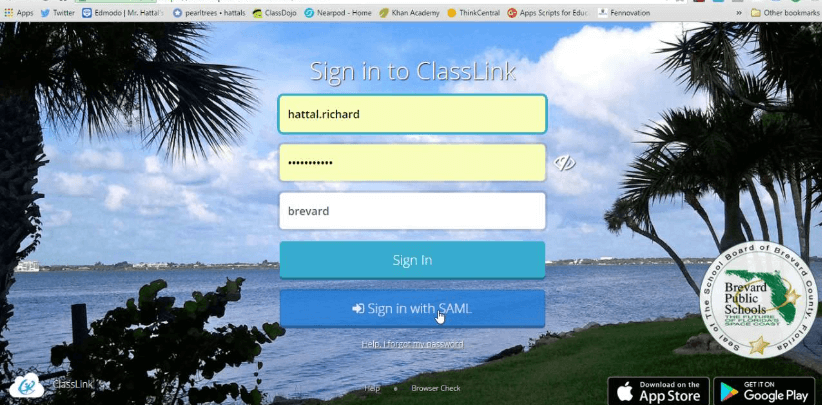
AWS Customer Support Policy for Penetration Testing
AWS offers many services that can be used for penetration testing, including Amazon EC², Amazon SNS, and Amazon SQS. AWS customer support will only provide support for penetration testing activities that are conducted following the AWS Customer Agreement and all other applicable laws.
By following these guidelines, businesses and organizations can ensure that their penetration testing activities are conducted safely and responsibly.
Conducting penetration tests without proper permissions can result in account suspension or termination. Therefore, customers must follow the AWS customer support policy when planning to conduct penetration tests.
Additionally, customers must obtain written approval from AWS before conducting any penetration tests against AWS resources.
Conclusion
Penetration testing is an important part of securing any computing environment, but it is especially critical in the cloud. By understanding what pen-testing is, why it matters, and what types of tests can be performed using AWS resources, businesses and organizations can ensure that their environments are secure and compliant with industry best practices.
Author Bio-
Ankit Pahuja is the Marketing Lead & Evangelist at Astra Security. Ever since his adulthood (literally, he was 20 years old), he began finding vulnerabilities in websites & network infrastructures. Starting his professional career as a software engineer at one of the unicorns enables him in bringing “engineering in marketing” to reality. Working actively in the cybersecurity space for more than 2 years makes him the perfect T-shaped marketing professional. Ankit is an avid speaker in the security space and has delivered various talks in top companies, early-age startups, and online events.
https://www.linkedin.com/in/ankit-pahuja/